BTC
$0.00
0.00%
The global world of cryptocurrencies, particularly Bitcoin and Ethereum, is growing rapidly. Alongside this, the number of crimes aimed at stealing assets and savings is also on the rise within the industry. According to data from private analytics firms and law enforcement agencies, in recent years alone, cybercriminals have stolen billions of dollars’ worth of various digital assets, using not only sophisticated technologies and vulnerabilities in user or service security, but also bot farms. In modern cryptocurrency theft schemes, bot farms are playing an increasingly significant role – large-scale networks of semi-automated and automated accounts that mimic human behaviour.
Experts regularly warn about the main methods of cryptocurrency theft, explain how digital ‘scam factories’ operate, and emphasise how to protect oneself from them and safeguard one’s investments or savings.
Experts stress that cryptocurrency is not stored ‘in a wallet’ in the conventional sense, and access to it is determined solely by the presence of a key. Improper storage of private keys leads to their loss or compromise, which means the complete loss of funds with no possibility of recovery. This is precisely why specialists recommend using hardware wallets, which store keys offline, significantly reducing the risk of online attacks.
So, among the main methods of cryptocurrency theft, the most common is phishing. Fraudsters create fake websites of well-known crypto exchanges or wallets, trick users into entering their passwords or seed phrases, and thus gain access to their assets and savings.
A separate but significant category of threats is the hacking of crypto exchanges. Such incidents demonstrate that even large platforms are not immune to flaws in their security systems. A striking, clear example was the attack on the Japanese exchange Coincheck, which led to the loss of over $500 million.
Among the common methods of theft, theft via malicious software is also prevalent. Computer viruses, Trojans and other malicious software can intercept information in the clipboard (when a user copies a wallet address), replacing it with the fraudsters’ address. They are particularly dangerous due to their stealth. Furthermore, criminals actively use fake apps. Fake crypto wallets have already been detected in app stores, through which, once installed, users’ funds were drained.
In addition, social engineering and the human factor have a significant impact on the development of crypto-crime. Many attacks are based on psychological influence and the manipulation of people. Fraudsters pose as exchange employees, technical support staff, or even relatives or friends. There are known cases where users were persuaded to quickly ‘check their wallet’, after which they themselves handed over access to their funds to the criminals.
There is a separate tactic – creating fake apps and ‘promoting’ them through fake ratings and comments. This is precisely how fraudsters trick victims into installing dangerous software.
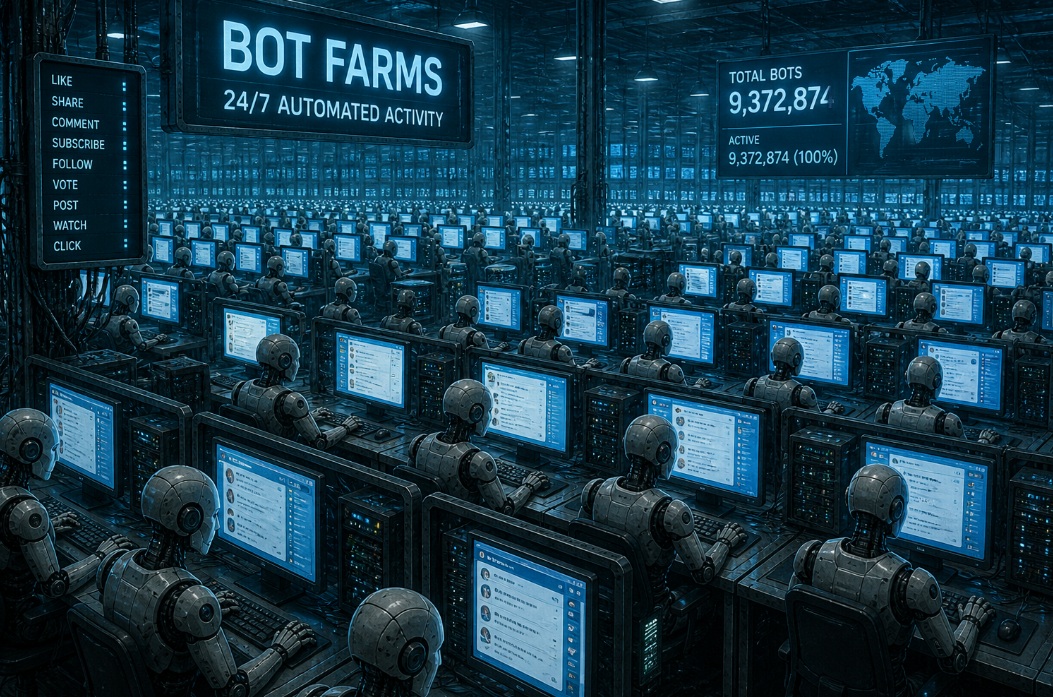
An infrastructure comprising thousands of fake profiles on social media, messaging apps and even crypto platforms is known as a bot farm. Bot farms can simultaneously disseminate identical messages, create a ‘mass effect’ and amplify fraudulent campaigns. Such networks are often centrally managed and use specialised software.
Fraudsters actively use bot farms for phishing attacks. They send out mass messages with fake links to services, leave positive reviews about fraudulent projects and impersonate the site’s technical support. As a result, the user, unfortunately, voluntarily hands over access to their assets.
To avoid falling victim to a bot farm, security experts recommend checking primary sources and not trusting mass ‘recommendations’ in comments, as this is a typical tool used by bot farms. Always treat links with caution, even if the website looks genuine. Bots often promote phishing sites, so always check the address manually. Minimise your ‘public profile’, as the less information there is online about your crypto assets, the lower the likelihood of becoming a target for bots.
Use ‘cold wallets’. For example, hardware devices from Ledger or Trezor make it much harder for anyone to access your funds, even in the event of an attack.
Remember: messages such as ‘your account will be blocked’ are almost always a classic social engineering ploy.
Cryptocurrencies open up a wealth of new opportunities, but at the same time shift the responsibility for security onto the users themselves. And unlike the banking system, there is no ‘customer support’ here to return your money.
Importantly, in most cases, token theft is the result of a combination of technical attacks and human carelessness.